White paper: Wireless data transmission to the Cloud via WiFi.
The Cloud (also known as Cloud computing) describes the provision of IT infrastructure, such as memory or software, via the Internet. For individual users, this means that you do not need to have your own server or to install any software for Cloud solutions. Depending on requirements, there are various Cloud models which differ in terms of scope of performance and data security. You will find out exactly what these are on this page.
The biggest advantage of the Cloud lies in its flexibility, because it is possible to scale services as required. There is also access to data in the Cloud from anywhere and with any internet-capable terminal device. Such flexible access to the Cloud is possible because there is a convenient technology for wireless data connection using WiFi. There are however several things to take into account with respect to data encryption and securing WLANs.
This white paper deals with the important standards and relevant security information.
What is a Cloud?
We come across the term "Cloud" everywhere nowadays and it therefore seems to be very new. However, it was coined in information technology right at the start of the 1990s to symbolize computer networks whose actual physical structure or mode of operation is irrelevant to users, but which appear to them like an individual computer.
The great advantage with respect to classic computers on or under your desk is that a Cloud computer grows flexibly with its tasks – memory, working memory and processors can be extended (scaled) as required.
However, first of all the term "Cloud" does not say anything about where this Cloud computer is located. In exactly the same way as there are rental and leasing vehicles, you can now also rent or lease computer capacities. In addition, these computers do not necessarily have to be in your own data center, but can be operated in any other location, as required. The only thing that is needed is a data link. The Internet is used as a data connection of this kind and is therefore often seen in direct relationship to the Cloud. We now all have more or less regular contact with Cloud computers via the Internet, without us necessarily being aware of this. These contacts for instance include online banking, ordering processes in mail-order business, accounts with e-mail providers or social media – all these daily processes would be inconceivable without the relevant Cloud in the background.
Cloud applications for data storage are particularly practical, especially when these data need to be used by different people or access to them needs to be from different locations. However, automatic backup to prevent data losses when there is a failure of your own hard disk may also be an influential argument in favour of using Cloud storage for many users.
A customized infrastructure is required to operate a Cloud. This may be very comprehensive, for example enabling a large mail-order company to process all the enquiries for their Christmas business. This "computer" is far too large on normal days in the year. What could be more logical then than to use these resources for other tasks and to share them with others?
This means it is only a small step to the business model of simply operating a Cloud and distributing the available capacities to lots of customers, as e-mail providers and social networks do, for example. The infrastructure is financed either via a regular user fee or the provision of cash-equivalent personal information, for example with social media.
Cloud service levels.
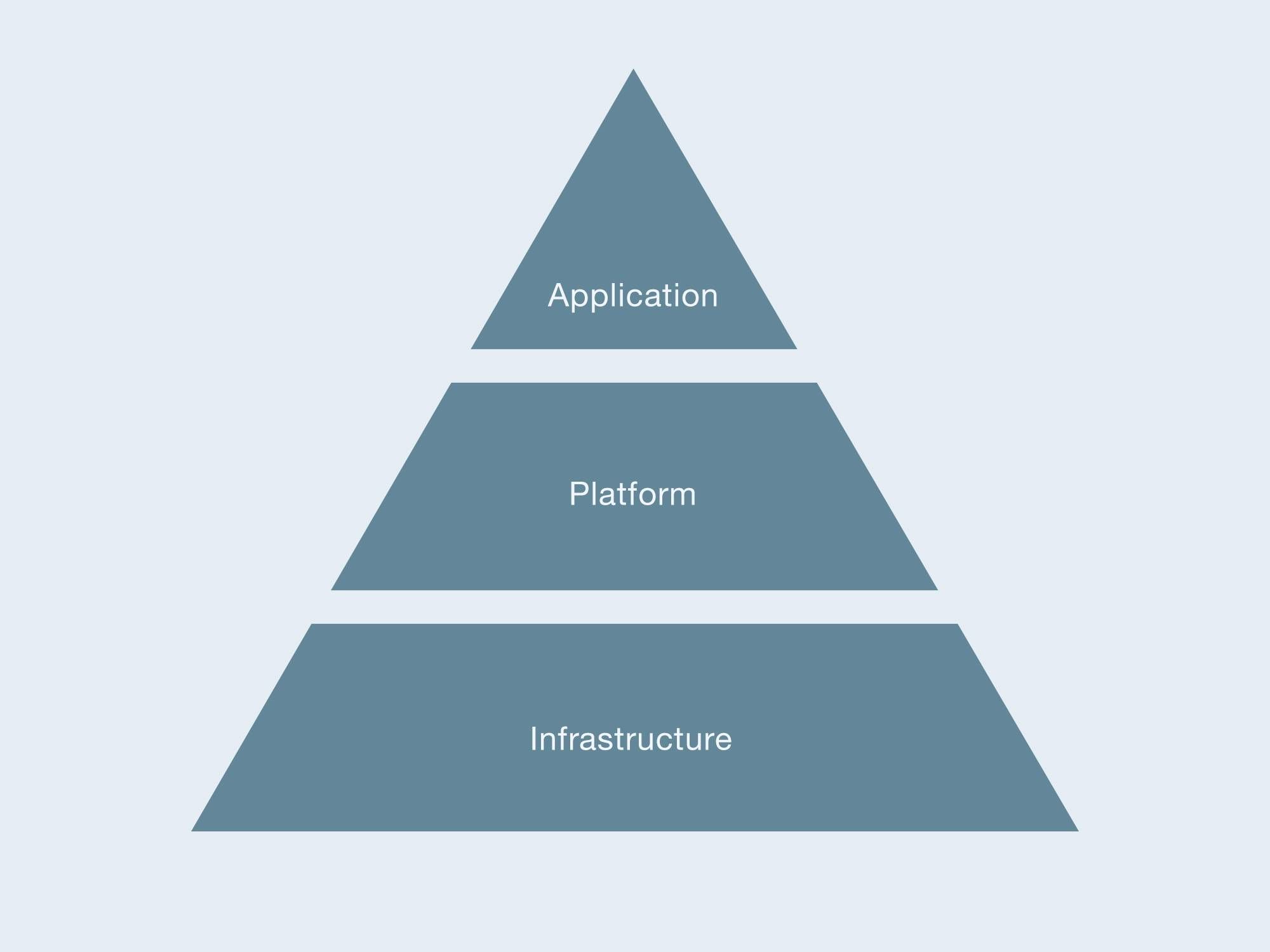
Infrastructure as a Service (IaaS)
Platform as a Service (PaaS)

Software as a Service (SaaS)
This allround worry-free package involves providing infrastructure, platform and the required applications. As a rule, the applications are accessed via a web browser, which means this does not depend on the platform used by the service recipient. A user fee is paid for usage and operation. For this, the service provider bears the acquisition and operating costs, including for complete IT administration, maintenance work, updates and backups.
Different Cloud models.
Public Cloud
Private Cloud
Community Cloud
Virtual Private Cloud
Communications and radio standards.
All Cloud offers require a data connection to the customer. When this is done via the Internet, it is correspondingly convenient and there are a really wide range of access options available.
The wireless connection of terminal devices such as notebooks, tablets and smartphones to the Internet is achieved either via the mobile telephone network or via WLANs. These Wireless Local Area Networks are local radio networks which are based on an international standard and have ranges of up to 100 m. There is an access point at the centre of a WLAN of this kind which forwards the WLAN radio link to the Internet either via cable or the mobile network. Access points of this kind are often also called (WiFi) hotspots or base stations.
IEEE 802.11
In order to allow smartphones, tablets and other devices developed within the framework of the Internet of Things (IoT) to make use of this technology everywhere, standards are needed for these radio links.
A working group of the IEEE began work on a standard for wireless networks in 1990. The Institute of Electrical and Electronics Engineers is a global professional association of engineers, mainly from the fields of electronics and information technology. It developed a protocol and transmission method for wireless networks. The IEEE 802.11 standard, established in 1997, was quickly accepted and spread rapidly. Building on that, this standard was continuously upgraded and improved. These upgrades can be identified by the appended lower case letters, such as a, b, g and n.
Because the 2.4 GHz band can be used without a licence in most countries, products according to the 802.11b/g standards have achieved widespread use. Other frequency bands are also used now: the 802.11ac standard uses the 5 GHz band, 802.11ad has led to the development of the 60 GHz band and 802.11ah is intended for the 900 MHz band.
The most important radio frequencies.
2.4 GHz
Advantages
- Gets through shielding materials with low losses – higher range
- Free-of-charge, authorized ISM frequency band
- Very widespread, low equipment costs
Disadvantages
- Frequency band has to be shared with other equipment or radio technologies (including Bluetooth, microwave ovens, baby monitors, cordless phones) leading to disturbances and interferences
- Problem-free use of a maximum of only 4 (USA: 3) networks possible at the same location, because effectively only 4 usable (scarcely overlapping) channels are available (in Germany: channels 1, 5, 9 and 13 – USA 1, 6 and 11)
5 GHz band
Advantages
- Significantly higher transfer rate
- Less used frequency band – low-interference operation
- Greater range, because 802.11h enables up to 1,000 mW transmission power – that more than compensates for the greater damping of the higher frequencies
Disadvantages
- Stricter regulations in Europe: dynamic frequency selection (DFS) is required on most channels, so as not to disrupt weather radar systems for example; no operation is permitted in the open air on some channels; if no automatic control of the transmission power (TPC - Transmit Power Control) is used, the transmission power has to be reduced
- Signal is quickly shielded by walls

Wi-Fi (Alliance)
Security in the radio network
Access to the access point
When a WLAN router is delivered, a standard password is pre-set for the router administrator. As a rule, this is publicly known, as the instruction manuals for the equipment are also available on the Internet. This means it is important to change both the administrator name and the associated password when commissioning. Many routers offer the possibility of addressing this via the Internet, logging in and making administrative changes. In most cases this function is disabled as standard. If there are no important reasons for enabling this function, it is advisable to leave the remote administration of the WLAN router disabled.
Each access point can or should have an individual name in order to differentiate it from other access points. This network name (SSID – Service Set Identifier) is generally broadcast by the access point and therefore visible to all potential users. If this access point is not intended to be visible to the public, the broadcasting of the SSID can be deactivated on the router. Users can nevertheless access it, but they need to know the name of the network to do so and cannot select it on their device from a list of the visible access points.
The choice of password is another step towards a secure WLAN. This is pointed out time and again, yet there are networks whose password is the same as the SSID or a sequence of numbers that is very easy to guess. Another possibility for making the unauthorized use of an access point more difficult is the so-called MAC (Media Access Control) address filtering. Every WiFi radio module has a unique MAC address which is stored as an identifier in the radio module and is used for identification in radio operation. The operator of an access point can store a list of the MAC addresses in the device of those devices to which they would like to grant access. When other radio modules attempt to make contact this is then rejected by the access point.
Another possibility for making the unauthorized use of an access point more difficult is the so-called MAC (Media Access Control) address filtering. Every WiFi radio module has a unique MAC address which is stored as an identifier in the radio module and is used for identification in radio operation. The operator of an access point can store a list of the MAC addresses in the device of those devices to which they would like to grant access. When other radio modules attempt to make contact this is then rejected by the access point.
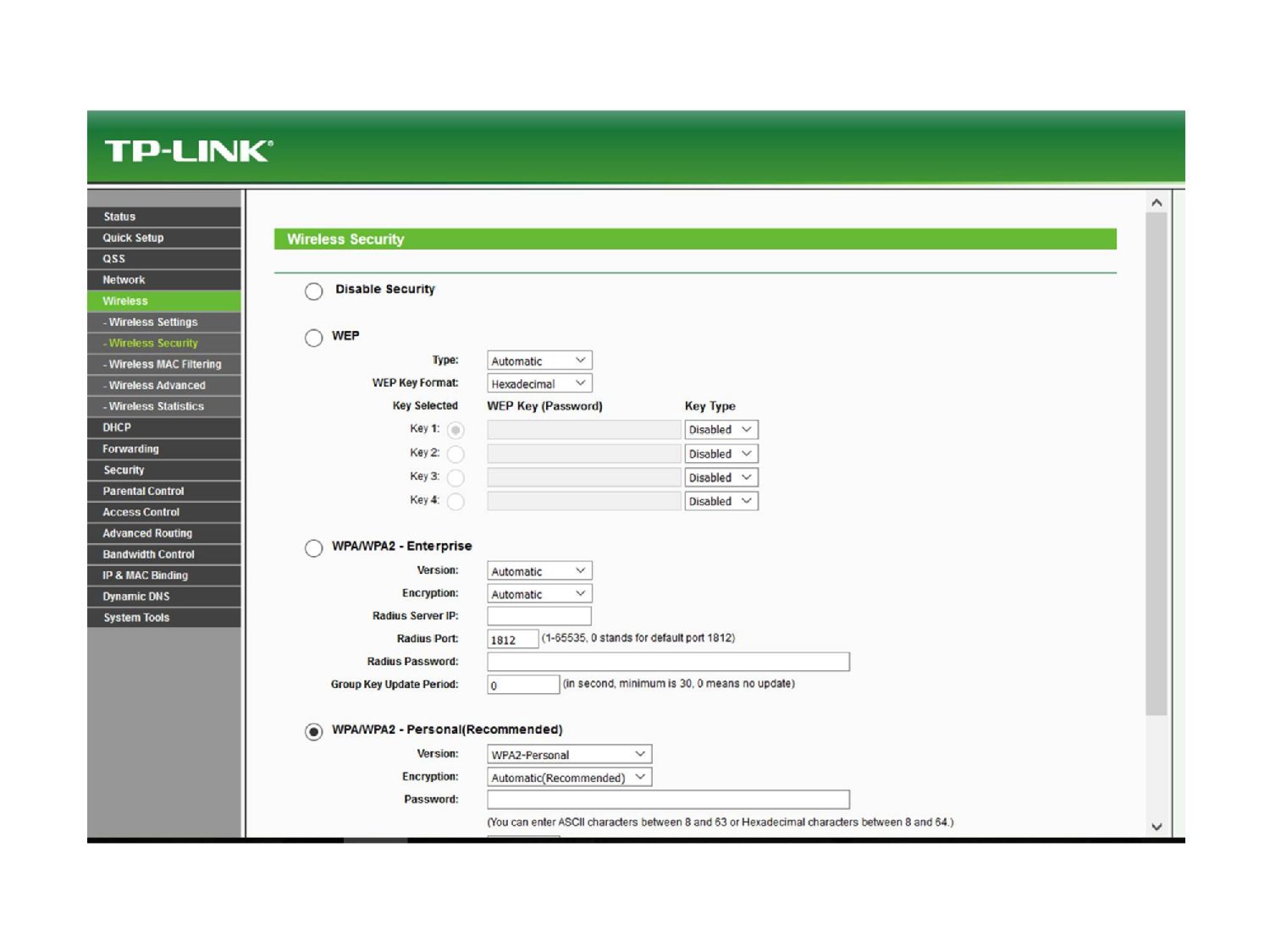
Encryption
Another important step towards ensuring a WiFi network against unauthorized use involves encrypting communication. All current WLAN routers have settings for this purpose. In the context of the ever more widespread use of WLAN technology, better and better methods for encrypting communication have been developed, because time and again weak spots have been detected making methods vulnerable. Simply for the sake of completeness, at this point it is necessary to name those encryption methods which are now considered to be insecure and should therefore no longer be used:
- WEP (Wired Equivalent Privacy)
- WPS (WiFi Protected Setup)
- WPA (WiFi Protected Access)
The current WPA2 (WiFi Protected Access 2) method is considered to be hard to get past, if appropriately secure passwords are also used. It is currently the security standard for radio networks according to the IEEE 802.11a, b, g, n and ac WLAN standards and is based on the Advanced Encryption Standard (AES). This method should therefore be used at the moment.
WLAN authentication
Conclusion.
Cloud computing enables private users, companies and public institutions to benefit from high-performance IT infrastructures, without having to purchase and operate these themselves. The "rent instead of buying" model gives you a considerable amount of flexibility in this respect. Because, in contrast to your own server farm, rented Cloud capacity can be scaled up or down as required. As a rule, the Cloud models which are currently on offer differ in terms of the scope of the resources made available by the provider and the required data security/privacy.
The fact that data and applications are stored or run in the Cloud (that is a computer or computer network somewhere in the world) enables the customer to call these up at any time from anywhere in the world on virtually any terminal device they like. This is particularly relevant in the so-called Internet of Things (IoT). This term describes the networking of different products with the Internet. The refrigerator that automatically orders milk is often mentioned in this context, but it only represents a fringe element, even if a very practical one. Intelligent production machines which can carry out automated ordering of materials are of much greater interest, as are data loggers which measure ambient conditions and give alarm notifications when limit values are violated.
However, the Cloud can only be used efficiently and conveniently through appropriate radio and communication standards. The most important here is Wi-Fi from the Wi-Fi Alliance. However, because wireless communication or data transmission can more easily be monitored or illegally used, a series of security measures are recommended. These range from password protection via encryption to WLAN authentication using MAC addresses. However, if you carefully decide on a suitable Cloud solution and also adhere to the latest security standards for the data link, there is nothing to prevent you making efficient use of these technologies.

Dr Volkmar Wismann.
Do you want to download the white paper as a PDF?
Register here with an e-mail address and we will send you a download link straight away.
Request here